ALL-IN-ONE PROTECTION WITH MDR FOR BUSINESS
Advanced Cybersecurity Services
Built for Real Business Risk
Alpha Secure delivers enterprise-grade cybersecurity services designed to protect critical data, sensitive information, and business systems from modern threats. Our approach combines advanced tools with human expertise to reduce risk, strengthen security posture, and build long-term resilience.

HOW IT WORKS
Managed Detection &
Response That Goes Beyond
Alerts
Alpha Secure is built around Managed Detection and Response, delivering cybersecurity services that actively investigate and neutralize threats in real time. Firewalls and alerts alone leave gaps. Our MDR services focus on identifying suspicious activity, validating intent, and responding immediately to reduce exposure and disruption.
Threat data is continuously analyzed across endpoints, servers, networks, and cloud platforms. Automated analysis works alongside experienced threat hunters to ensure accuracy and speed.
AI-Powered Detection
Continuous monitoring across all endpoints and networks using advanced machine learning algorithms.
Human Threat Hunting
Expert security analysts validate alerts and investigate suspicious activities.
Immediate Response
Automated and manual containment actions to neutralize threats before damage occurs.
SERVICE CATALOG
Core Cybersecurity Services
Safeguards computers, servers, and mobile devices against malware, malicious code, and suspicious activity in real time.
Protects mission-critical systems that process payments, store customer information, and manage internal resources.
Verifies every connection attempt – checks user permissions, device integrity, and network security before granting access.
Protects data on lost or stolen laptops, servers, and mobile devices – encrypted data remains unreadable.
Uses machine learning and behavioral analysis to identify phishing attacks and malicious activity early.
Secures access to cloud-based services, collaboration tools, and monitors user behavior to prevent breaches.
Protects against phishing scams, fraudulent links, and social engineering attacks with advanced filtering.
Identifies and tests security weaknesses before attackers can exploit them.
Correlates activity across endpoints, servers, cloud, and networks to improve visibility and accelerate response.
Providing continuous threat monitoring, proactive detection, and rapid response to safeguard systems against advanced cyberattacks.
24/7 assistance to keep business systems stable, secure, and operational with direct access to technical professionals.
Reduces risk of unauthorized access by requiring more than a password.
PRICING
Core Cybersecurity Packages
Available Alpha Secure Endpoint Packages
Includes: Endpoint protection, threat detection, 24/7 monitoring, and incident response.
Get Endpoint QuoteAvailable Alpha Secure Server Packages
Includes: Server hardening, vulnerability management, backup verification, and compliance reporting.
Get Server QuoteSECURE WHITEPAPERS
TRUST & EXPERTISE
Secure With Sensitive Data
Alpha Innovations delivers cybersecurity services backed by real-world experience, proven tools, and continous oversight. Our team manages critical data with detection, response, and optimization so clients can focus on operations rather than security alerts. The result is stronger protection, reduced downtime, and greater confidence in day-to-day technology use.
Proven Experience
Years of protecting critical business data
Continous Oversight
24/7 monitoring and threat management
Reduced Downtime
Rapid response minimizes business disruption
Operational Focus
We handle security so you handle business.
Enterprise-Grade Security
Fortune 500 level protection
Scalable Solutions
Grows with your business needs
Dedicated Team
Direct access to security experts
TECHNICAL DETAILS
System Requirements & Integrations
Supported Endpoints
- Windows 10/11 & Server 2016+
- macOS 10.15+
- Linux (Ubuntu, RHEL, CentOS)
- iOS & Android devices
Cloud Integrations
- Microsoft 365 & Azure AD
- Google Workspace
- AWS & Azure Cloud
- Salesforce & Slack
System Requirements
- 2GB RAM minimum per agent
- 500MB disk space
- Internet connection (SSL/TLS)
- Admin rights for installation
Supported Integrations & APIs
SIEM
Splunk, QRadar, Sentinel
PSA
ConnectWise, Autotask
RMM
N-able, Kaseya
ITSM
ServiceNow, Jira
Secure Frequently Asked Questions
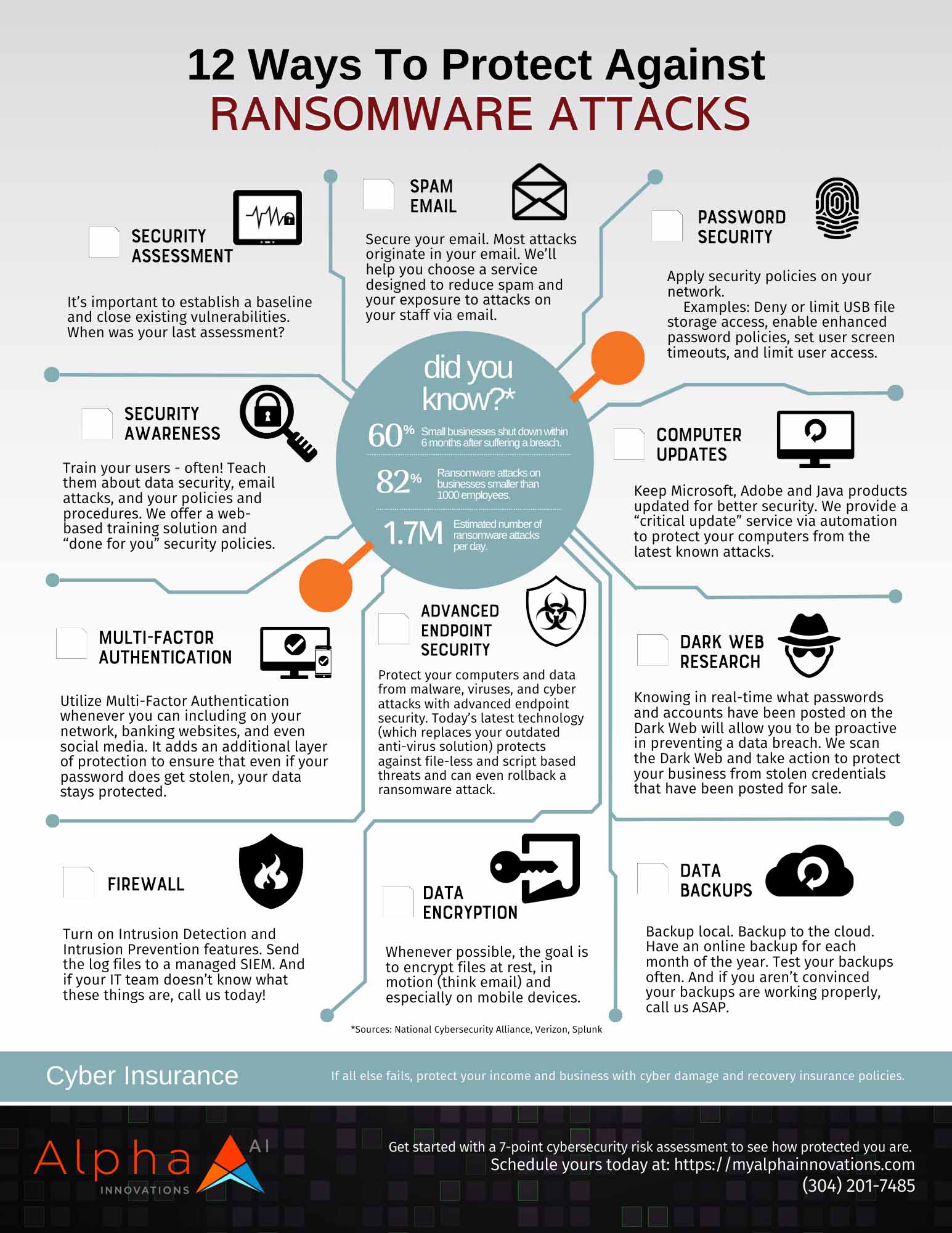
Cybersecurity services protect business systems, networks, and sensitive data from threats like ransomware, phishing, and unauthorized access. Alpha Secure combines monitoring, threat detection, and response to reduce risk and maintain continuity.
Managed cybersecurity services provide continuous monitoring and expert response, not just alerts. Alpha Secure includes human-led threat investigation and active mitigation rather than relying solely on software.
Alpha Secure reduces breach risk through endpoint security, access controls, vulnerability management, and real-time monitoring. These layers work together to detect suspicious activity early and stop threats before data is exposed.
Yes. Alpha Secure scales to support small businesses, mid-market organizations, and public sector environments. Service levels are designed to match operational needs without unnecessary complexity.
Endpoint security protects laptops, servers, and mobile devices that access business data. Alpha Secure monitors device behavior to prevent malware, credential misuse, and unauthorized access.
Alpha Secure follows a structured incident response process that includes investigation, containment, and remediation. Human-led threat hunters validate activity before taking action to minimize disruption.
Alpha Secure follows principles aligned with the NIST Cybersecurity Framework, focusing on risk management, detection, response, and recovery. This approach supports compliance and long-term resilience.
Getting started begins with understanding your current environment, risks, and business goals. Our team reviews systems and recommends appropriate protection based on real-world threats.

Want to talk to an expert?
Alpha Innovations is committed to protecting your data. Please review our Privacy Policy for information on how Alpha handles personal data and your rights concerning it. By submitting this form, you agree to the storing and processing of your data by Alpha as described in the Privacy Policy.
"*" indicates required fields

Alpha Innovations simplifies complex technology into practical business solutions. We manage IT, communications, security, and backup systems – so you can focus on growth while staying fast, secure, and resilient in a changing market.
BUSINESS INFO
Mon-Fri:
8:00AM- 5:00PM
Sat: Closed
Sun: Closed
Phone:
(304) • 201 • 7485 – Helpdesk
(304) • 201 • 2616 – Sales
E-mail:
salesgroup@myalphainnovations.com
marketing@myalphainnovations.com
NEWSLETTER/SOCIAL MEDIA
"*" indicates required fields
HEADQUARTERS
DATA CENTER 1
Copyright © 2025 Alpha Innovations, All Rights Reserved | Privacy Policy | Cookie Policy | Site Map | MSA